## Problem 2 – CSP
Consider the following constraint satisfaction problem. A linear graph has nodes of the following colors:
– Red
– Yellow
– Green
– Blue
– Violet
Each node has a domain of {1, 2, …, 9}.
Each node type has the following constraints on its value:
– Red – No contraints
– Yellow – equals the rightmost digit of of the product of all its neighbors
– Green – equals the rightmost digit of the sum of all its neighbors
– Blue – equals the leftmost digit of the sum of all its neighbors
– Violet – equals the leftmost digit of the product of all of its neighbors
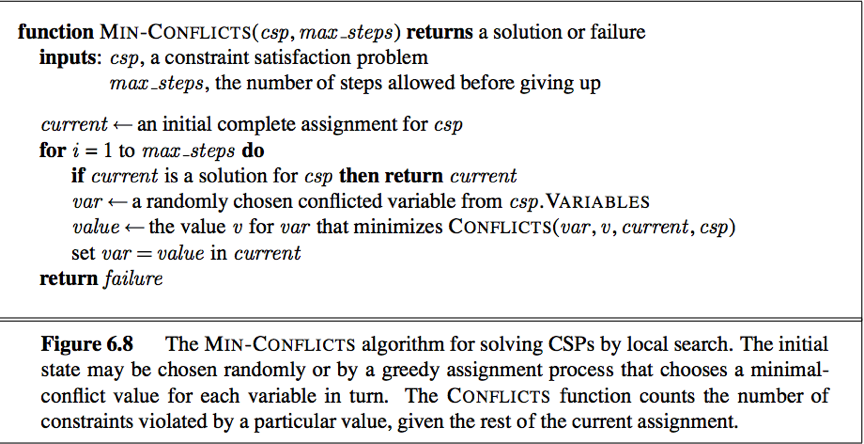
As a reminder here is the pseudo code for the Min-Conflicts search algorithm:
**Notes:**
– It’s possible that you won’t converge to a solution in a single run. Try a few runs to see if you get to a solution.
– The example is to show you what a problem looks like, we will test/grade your program on different examples
Complete the function *solve_csp* defined below. You may find some helper functions useful.
