This is the second section of your research report, you will be writing the first part of your deep research. This means, that what you put in this section will be determined by you. You can talk about the subject in detail, compare your topic to another one, etc. This section should be between 3-5 pages with appropriate references added.
Help2
IPsec and DNSSEC to enhance the protection of the domain. Note: IPsec is a security protocol that provides network-based authentication and confidentially between servers via a set of standards, while DNSSEC is a set of extensions that provide integrity to the DNS server to aid in deterring attackers from hijacking the DNS process.
Using the above enterprise architecture scenario, which consists of different components (e.g., servers, clients, databases) with information that has various temporal and distribution constraints, networks, multiple sites, and trusted and untrusted clients, write a 500- to the 750-word summary, making sure to:
- Describe the appropriate cryptographic tools/algorithms/protocols that can be applied at various locations throughout that architecture in order to achieve a variety of goals.
- Define the purpose of IPsec (including the various modes, IKE, ESP vs AH, Windows firewall integration, and IPv6) and DNSSEC (relationship to PKI, DNS Zones, and trust anchors).
- Briefly describe what you accomplished from the procedures supplied, and how these protocols enhance the security of servers. Provide references to recent articles (less than a year old) that demonstrate the use and benefits of an organization that has implemented IPsec and DNSSEC.
- Describe the management challenges/tradeoffs associated with implementing various security controls and protocols in an enterprise network.
NOTE: Each question should be a heading
File Processing Mod 1
*** Must Use Eclipse***
SLP Assignment Overview
Write a Java application to accomplish the following task:
- Ask users to input the amount of tax they paid for the past 3 years.
- Write this information to a text file.
Once you finish the assignment, copy the Java program along with a screenshot of the output and paste it into a Word document. Submit the Word document to the SLP 1 dropbox.
SLP Assignment Expectations
- Use proper data structures in the program.
- Know how to write data to a text file.
- Use proper exception handling techniques to protect against file I/O errors.
Macintosh Forensics
Learning Objectives and Outcomes
- Describe the capabilities of three tools used to recover deleted Macintosh files.
- Recommend one of the tools for use in a given scenario.
Assignment Requirements
You are an experienced digital forensics specialist for DigiFirm Investigation Company. One of your clients is a small music production company. One day you receive a phone call from Andrea, the owner and president of the music company.Andrea believes one of her employees, a sound technician, has been stealing intellectual property from the company. She thinks he is copying original music scores and then selling them to upstart musicians, claiming that he wrote them. Andrea checked the employee’s computer the previous night and thinks he has been deleting the files to cover his tracks. He uses a Macintosh computer.There are several tools available for recovering files that have been deleted from a Macintosh computer, including:
- MacKeeper, https://mackeeper.com/
- Mac Undelete, http://www.macundelete.com/
- Free Undelete Mac, http://www.freeundeletemac.com/
For this assignment:
- Research three specific tools that can aid in recovering deleted Macintosh files.
- Write a report about the capabilities of the tools.
- Recommend one of the tools for use in this case and justify your recommendation.
Required Resources
- Course textbook
- Internet
Submission RequirementsFormat:Microsoft WordFont:Arial, Size 12, double-spaceCitation Style:Follow your school’s preferred style guideLength:1-2 pages
Self-Assessment Checklist
- I researched three specific tools that can aid in recovering deleted Macintosh files.
- I described the capabilities of the tools.
- I recommended one product for use in this case and justified my recommendation.
- I created a professional, well-developed report with proper documentation, grammar, spelling, and punctuation.
4/3 Discussion
- Read Chapters 14–17 in your textbook.
- Using the discussion link below, respond to the following prompts and questions:
- What types of threats can impact operations of the infrastructure? What steps can be taken to protect systems in the infrastructure (server or desktop systems and beyond)?
- How can threats from Internet-based activities, such as the use of e-mail and web browsing, be mitigated? What is the responsibility of the user community in mitigating such threats?
- Your initial post should be at least 300 words and supported with at least three references.
data analytics
It is the aim of data analytics to produce accurate predictions that are of great value to clients or constituents . Sometimes however these predictions turn out to be wrong for a variety of reasons. Can you think of a case where data was analyzed and a prediction made that turned out to be a colossal mistake?
4/4 Assignment
- Paper on Mitigation Strategy
- Phase 2 of Final Project: Provide a comprehensive mitigation strategy based on the threat analysis done in Assignment 2.4.
- As mentioned in Assignment 2.4, you may use a fictitious company, one that you researched on the Internet, or your own workplace (with an alias used for the company name).
- Conduct Internet research for formats that are used for developing and categorizing a security mitigation strategy.
- Include a short executive summary for this assignment, which you will revise later for use in the final paper.
- The mitigation strategy should be approximately 4 to 5 pages in length, in APA format, and double-spaced for the narrative.
- You may use tables or other graphic representations; however, these additions to the paper should not be included in the page count.
- The paper should include references to any material used in preparing the paper. You should use online resources to develop your plans; just make sure to cite these sources.
Task A2- Diss Ch 1 and 3 help
Ch 1 and 3 help
1.9 LAB – Query execution plans (Sakila) coding
1.9 LAB – Query execution plans (Sakila)
This lab illustrates how minor changes in a query may have a significant impact on the execution plan.
MySQL Workbench exercise
Refer to the film, actor, and film_actor tables of the Sakila database. This exercise is based on the initial Sakila installation. If you have altered these tables or their data, your results may be different.
Do the following in MySQL Workbench:
- Enter the following statements:
USE sakila;
SELECT last_name, first_name, ROUND(AVG(length), 0) AS average
FROM actor
INNER JOIN film_actor ON film_actor.actor_id = actor.actor_id
INNER JOIN film ON film_actor.film_id = film.film_id
WHERE title = "ALONE TRIP"
GROUP BY last_name, first_name
ORDER BY average;
- Highlight the SELECT query.
- In the main menu, select Query > Explain Current Statement.
- In the Display Info box, highlighted in red below, select Data Read per Join.
Workbench displays the following execution plan:
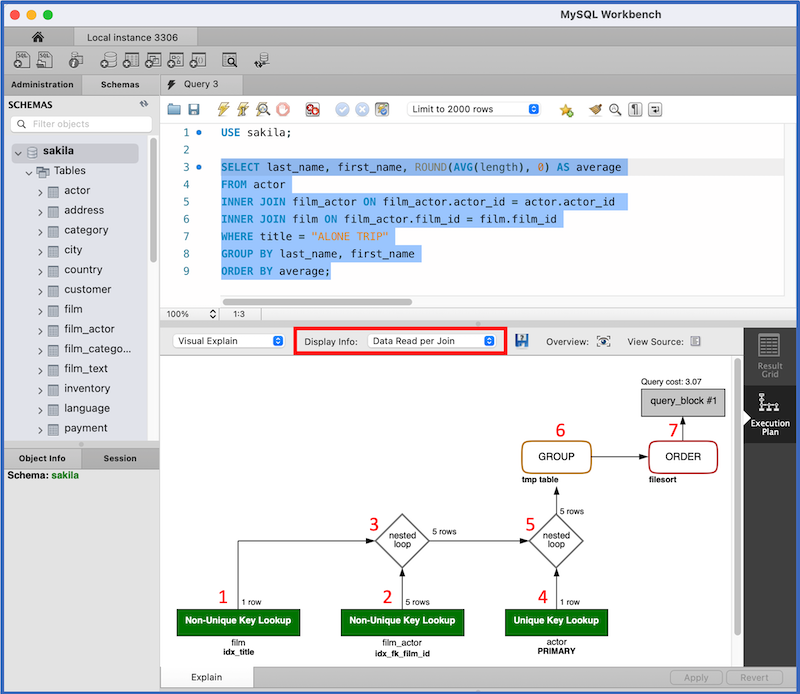
The execution plan depicts the result of EXPLAIN for the SELECT query. The execution plan has seven steps, corresponding to the red numbers on the screenshot:
- Access a single
filmrow using theidx_titleindex on thetitlecolumn. - Access matching
film_actorrows using theidx_fk_film_idindex on thefilm_idforeign key. - Join the results using the nested loop algorithm.
- Access
actorrows via the index on the primary key. - Join
actorrows with the prior join result using the nested loop algorithm. - Store the result in a temporary table and compute the aggregate function.
- Sort and generate the result table.
Refer to MySQL nested loop documentation for an explanation of the nested loop algorithm.
Now, replace = in the WHERE clause with < and generate a new execution plan. Step 1 of the execution plan says Index Range Scan. The index scan accesses all films with titles preceding "ALONE TRIP", rather than a single film.
Finally, replace < in the WHERE clause with > and generate a third execution plan. Step 1 of the execution plan says Full Table Scan and accesses actor rather than film.
zyLab coding
In the zyLab environment, write EXPLAIN statements for the three queries, in the order described above. Submit the EXPLAIN statements for testing.
The zyLab execution plans do not exactly match the Workbench execution plans, since this lab uses a subset of film, actor, and film_actor rows from the Sakila database.
NOTE: In submit-mode tests that generate multiple result tables, the results are merged. Although the tests run correctly, the results appear in one table.
Unit 5 DB: Data Mining and Business Intelligence
Your friends John and Pam’s business has been expanding at a very fast pace. At this phase, they want to broaden their business scope and sell packaged meals at grocery stores and online. You have mentioned to them the importance of data mining and business intelligence in today’s business, and they have asked you to explain the following:
- Data mining and online analytical processing and how it applies to their business model.
- The adoption of business intelligence techniques and their benefits to John and Pam’s organization.
In response to your peers, explain how these concepts are used in today’s marketing.
